PC Water Cooling for High Performance Computing in Science Research
April 2022
 My water cooled high performance computing rig for astronomy research – 10 fans, 3 radiators, AMD Ryzen 9 3900XT CPU, Nvidia RTX3090 GPU and RTX2060 Super GPU
My water cooled high performance computing rig for astronomy research – 10 fans, 3 radiators, AMD Ryzen 9 3900XT CPU, Nvidia RTX3090 GPU and RTX2060 Super GPU
TOC
1. Intro 2. The Benefits of Water Cooling for High Performance Computing 3. Isn’t This Some Kind of Cryptocurrency Mining Rig? 4. Risks, Cost, Emissions and Waste 5. Water Cooling Loop Design and Components 6. Water Cooling Parts 7. High Performance System Parts List 8. But Why Don't You Just... 9. Single versus Dual Loop 10. How Many Radiators Do You Need? 11. AIO vs Custom Loop 12. Flushing all parts out with Distilled Water 13. Temperature and Flow Monitor 14. Tubing 15. Fans and Airflow 16. VRM, RAM, PCH and NVMe cooling 17. Reservoir and Pump 18. Coolant 19. RGB Lighting 20. Coil Whine
1. Intro
Earlier this year I wrote about how you can contribute your PC's computing power (and part of your electricity bill) to distributed volunteer cloud computing for science research https://blog.ajflynn.io/become-part-of-a-global-super-computer-network-for-astronomy-research
This kind of high performance computing can place extreme demands on a PC's cooling system. The CPU and GPU may be run at the limits of their power consumption, 24/7, producing far more heat than standard gaming or business usage ever would.
In this article I'll share some thoughts and experiences from my recently completed project to install water cooling in my home PC, which I use for day to day gaming, as well as for volunteer cloud computing when it is idle.
While the following advice is focused on a system designed for high performance computing for science research applications, the information may still be useful for those looking to add water cooling to their PC for gaming use.
For more detail about water cooling setups and components in general, check out this excellent guide by EKWB https://www.ekwb.com/guides
2. The Benefits of Water Cooling for High Performance Computing
Water cooling has a number of advantages over air cooling for high performance science research applications:
- Air cooling alone may be unable to sufficiently cool parts inside an enclosed PC case with the CPU and GPU(s) running at 100% power load for extended periods of time. This is a situation that would rarely be encountered while gaming or during normal computer use.
- Systems running more than one GPU may have insufficient space to allow the GPU stock air coolers to operate efficiently, and the GPUs may even block each others fan inlets entirely.
- Air cooling may be extremely loud, as a large number of fans may need to be running at high speed. GPU onboard fans are especially loud as they are quite small but must move large volumes of air. Noise isn't a big issue in a data center or dedicated server room, but is a nuisance when the PC is in a home or office environment.
- It is important to note that water cooling will not cause your PC to produce less heat. It will simply move the heat away from the hot internal components and dissipate it into the air in your room more efficiently. This can allow components to operate at the peak of their power capability without overheating, and operate more quietly, which may not be possible with air cooling alone.
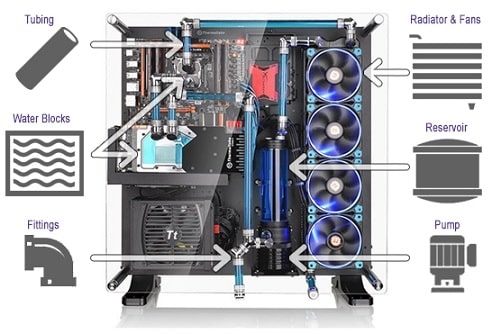 Water cooling parts. Image by https://www.build-gaming-computers.com
Water cooling parts. Image by https://www.build-gaming-computers.com
3. Isn’t This Some Kind of Cryptocurrency Mining Rig?
Water cooling doesn’t make sense for cryptocurrency mining. An open-air rig that is cooled by fans alone is much more cost effective than water cooling. For that kind of computational work, you’re trying to maximise output while minimising cost, and you don’t care if it’s noisy. A mining rig is easier to position in a garage or other out-of-the-way spot where the noise it produces won’t be so much of an issue.
4. Risks, Cost, Emissions and Waste
Before rushing in to contributing your PC’s idle time to cloud computing for research, or water cooling your PC, you should consider the following:
- Everything we do consumes resources, creates waste and produces emissions. Aiming to reduce these factors helps to ensure we have a sustainable society, where we can keep doing the things we want to do, with minimum negative consequences in our lifetime or the lives of future generations.
- We don't absolutely need to investigate the universe around us through the science of astronomy. Life would continue without it. But science research, art, recreation such as gaming and any number of other “non essential” human activities arguably make life better for everyone. Astronomy is contributing to our knowledge and understanding of the universe around us, and the knowledge gained is shared with all mankind. Astronomy also leads to technological advances and benefits in other aspects of human life. This is arguably a more beneficial pursuit than burning fuel, creating carbon emissions and e-waste to support the digital mining of Cryptocurrency, which serves no other purpose than increasing some individuals’ wealth, for instance.
- Running your PC on high performance computing tasks 24/7 will increase your power bill, and your carbon emissions footprint, whether you use water cooling or not.
- If you have access to a renewable energy source, such as solar power, the environmental impact and cost of 24/7 high performance computing may be greatly reduced.
- On the positive side, simply adding water cooling will have minimal impact on power consumption on its own. You're just adding a few extra fans and a small water pump. Water cooling won't change the power consumption of your PC components by itself, but it may allow you to run those components at a higher wattage for gaming or science research purposes.
- Water cooling is difficult, costly, may void the warranty on your GPU. In general these days, GPU manufacturers will usually consider returns for faulty GPUs that have had water cooler installs done correctly, as long as installing the cooler isn’t what caused the GPU to malfunction. But there is no guarantee this will be the case.
- Water cooling also carries risks such as the potential for a water leak to destroy expensive electronic components. While leaks are unlikely when the hardware is installed correctly, and leaks are unlikely to actually destroy your equipment (usually it just creates the need for a tedious cleanup), they are still a risk factor.
- Are you considering water cooling just because it looks awesome or is a fun hobby? I don't think there's anything wrong with doing things just because they are aesthetically pleasing or fun to do, but you should carefully weigh up the potential risks and cost when it is a hobby rather than a practical need.
- Running your PC on high performance computing tasks 24/7 can contribute to heating your house during winter, which is a benefit. But this will be offset by the need to cool the house more in summer (leading to more use of the air conditioner, for instance).
- The basic laws of thermodynamics dictate that one Watt spent on computing power equals that same Watt of energy being turned into heat that ultimately ends up in the air surrounding the computer. Energy is never “used up”, it just gets moved somewhere else.
- I found that the amount of plastic and cardboard waste from purchasing all the individually boxed and wrapped water cooling parts was alarming. However, I was able to recycle the cardboard and hard plastics which make up the majority of the packaging materials. In Australia you can drop off soft plastics such as bags for recycling at Woolworths or other locations (check with your local council).
- Cardboard and many types of hard plastics can of course be recycled in your usual domestic recycling bins. Please check your local council recycling advice. The specific plastic types that can be recycled in domestic recycling bins and what you need to take to special drop-off points differs greatly by council and suburb, even between neighbouring suburbs within the same city.
 My water cooling loop, which cools 2x GPUs, 1x CPU using 3 radiators.
My water cooling loop, which cools 2x GPUs, 1x CPU using 3 radiators.
5. Water Cooling Loop Design and Components
Some thoughts on loop design and component choice:
- Consider where everything will fit. Water cooling components take up a lot of space. If your computer case doesn't already have special places to attach radiators, then you will probably need a new case before you can install water cooling. I highly recommend the Lian Li O11 series of cases for their flexibility, modularity, dedicated radiator mount points and large amounts of space. It is possibly the most popular case for new water cooling builds at this time. The case I am using is the Lian Li O11 Dynamic.
- The most likely issue you will have with space is getting the GPU, radiators and the reservoir to fit together in the space you have available, as these are the bulkiest items. Be sure that the placement you have in mind within your case really works with the measurements of all these components. Be prepared to have to change your plans when you get the equipment, and to exchange parts or get a different case, etc. Things simply may still not fit as you expected, even after careful planning.
- GPUs may actually become smaller in some dimensions when switching the coolers to water blocks, as you remove the bulky stock air cooler. Check out the water block dimensions on the manufacturer's site to determine the amount of space your GPU will need once it has a water block installed. Even in the roomy Lian Li O11D case, I was only able to fit the reservoir in the mounting position I chose, because the RTX3090 GPU was made several centimeters shorter when the water block was installed. However, the height of the RTX3090 plus its water inlet and outlet riser was far greater than I expected. The case lid cleared the water block by less than 1mm when closed. I didn't check the card and water block height, as I was focused entirely on its length and potential collision with the reservoir. Thankfully the O11D case is very roomy, so I got away with it.
- Component order in the loop doesn’t matter. Your loop could run coolant from the pump to the GPU, then to a radiator, then to the CPU, then to another GPU, then another radiator. Or any other order you choose. The water is moving so fast through the loop that it’s more like a single pool of liquid that each component happens to be sitting in. CPUs and GPUs add heat to the pool. Radiators take heat out of the pool. The pump keeps the liquid in the pool stirred up and moving.
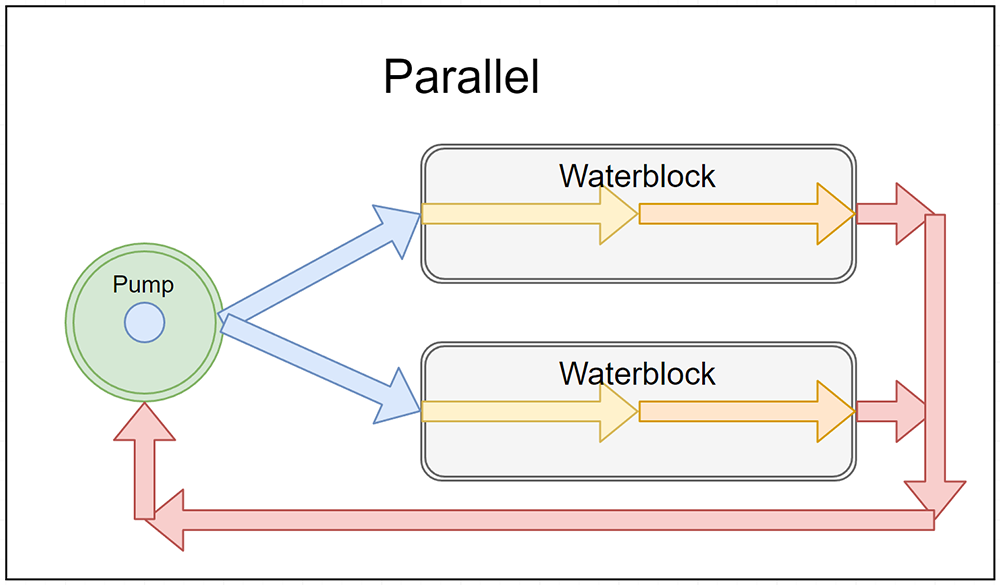
- A parallel loop setup is better than series, when it comes to high performance computing. Parallel hookup of the cooling blocks allows highest possible flow through each water block. The difference between series and parallel connections is minor in a gaming setup but noticeable for high performance setups. In a series water block setup, the flow rate will be limited by how much water the single most restrictive water block will allow through at any given pump pressure. In a parallel water block setup, the flow rate will be limited by the sum of what each water block will allow through at any given pump pressure. As a result, the parallel setup flow rate will always be higher.
- My cooling loop uses a hybrid of parallel and series connections (see diagram). The CPU and two GPUs are connected in parallel to the loop, as their water blocks are the most restrictive components on water flow. The radiators and pump are connected in series.
My custom loop is a single combined loop with 3 radiators (one thick and two thin radiators). My high performance computing setup needs to dissipate 800W+ of heat when the CPU and GPUs are overclocked. The loop cools an AMD Ryzen 9 3900XT CPU, an Nvidia RTX3090 GPU and RTX2060 Super GPU.
As I run two GPUs and a high-end CPU at full power 24/7, I purchased a new 1200W Power Supply Unit (PSU) to replace my old 850W PSU. This allows about 50% headroom over the max combined wattage of all the components running at full power. I understand that as little as 25% headroom is still fine.

6. Water Cooling Parts
The basic parts needed for a custom water cooling loop are:
- Radiators. These try to bring the water back to room temperature by dissipating the heat into the air.
- Fans. These move air through the radiators to cool them.
- Tubing. I recommend using soft tubing at first so you can easily experiment and change your setup. You can get hard tubing too, which looks nicer and can be bent at 90 degrees where required, but it is a lot harder to work with and change.
- Reservoir. A tank that contains extra coolant that typically sits directly above the pump.
- Pump. This moves the coolant around the system.
- Barbs. If you choose soft tubing for your loop, barbs are fittings that you can squeeze the ends of tubes on to that will hold the tubes without the need for clamps or collars. But I recommend you use clamps on all barbs, as I found that if you bump a tube connected to a barb fitting, it can leak a bit of fluid. I used standard household cable ties.
- Right angles. These fittings allow you to connect tubes at right-angles to the coolant sockets on water blocks, pumps, etc. Mostly useful when used with soft tubing, which doesn’t like to be bent at 90 degrees.
- Water blocks. These are the coolers that go on the GPU or CPU to run coolant past a special water cooling heat sink attached to the core of the hot device. Water blocks completely replace the air coolers that are normally attached to these devices. NOTE: Be sure to get exactly the right water block for your GPU or CPU type, or it won't fit. Make sure your exact CPU socket type or GPU model are listed as compatible with the water block on the manufacturer's website!
- Flow and temperature meter. Not essential, but I highly recommend one as it lets you see exactly what is happening in your cooling loop in response to changes you make to the layout, or the loads and stresses you put it under. Many include an audible alarm to warn you when water temperature or coolant flow are at unacceptable levels.
- Coolant. Ideally a pre-made mixture usually made of distilled water, anti-rust and anti-algal agents that is used to fill your water cooling loop. Pre-mixed coolant is readily available from MWave and similar stores. See more info in the Coolant section below.
- Cables. You will likely need extra cables to allow for the multiple fans the radiator(s) will need (such as fan cable splitters and extenders). RGB fans and RGB water blocks add to this requirement twofold, as they each have double the cables leading to them (one for power and one for RGB) and you need to somehow connect potentially dozens of cables to just a few fan and RGB connections on a motherboard, that they may not reach on their own.
- RGB controllers & fan controllers. May not be required, depending on your setup, but it's something to consider. Many water cooling parts, fans, etc will come with controllers, so check what is included before buying separate controllers.
7. High Performance System Parts List
The following is a list of the components I purchased for my system, to give you an idea of what is required in a custom high performance water cooling loop, to cool a one CPU and two GPUs, that are expected to run 24/7 at maximum wattage. I didn't use every single part listed, as I got some extra fittings (such as barbs or right angle adapters), just in case.
I didn't purchase it all at once. I purchased the basics first (and started out with just one radiator), then had to get additional fittings and additional radiators as I worked out what I needed to improve cooling performance to an acceptable point, and to make some of the connections and pipe routing more efficient and elegant.
I did not need to purchase new NVMe drives, CPU, RAM, GPUs or motherboard, as the ones I already owned were adequate.
The total cost for the parts I required to make this cooling loop, including the extras such as a new PSU, ended up being around $3,300.
For a more traditional single loop cooling 1 GPU and 1 CPU, with one radiator, the cost for the water cooling parts alone would be more like $1,500.
Prices are in AUD and include GST, but exclude shipping.
From MWave https://www.mwave.com.au/
AC14686 Thermaltake Pacific CL360 360mm Radiator (64mm thickness) x1 $159.00
AC19474 Thermaltake Pacific C360 360mm Radiator (27mm thickness) x2 @ $129.00ea $258.00
AC50178 Thermaltake Pacific PR12-D5 Plus Pump & Reservoir Combo w/ RGB Software Control x1 $339.00
AC38261 Thermaltake TOUGHFAN 12 120mm High Static Pressure Radiator Fan [SINGLE FAN] x3 @ $39.00ea $117.00
AC49086 be quiet! Light Wings ARGB 120mm PWM Black Case Fan – [TRIPLE PACK] x2 @ $105.00ea $210.00
AC37179 Thermaltake Pacific TF2 Temperature and Flow Indicator – CL-W275-CU00SW-A x1 $79.00
AC11819 EKWB Filling Bottle (1000mL) x1 $13.99
AB61483 Thermaltake V-Tubler 3T Flexible Tubing 3/8” (9.5mm) – 2m x2 @ $15.00ea $30.00
AC22192 Thermaltake TT Premium T1000 1L Transparent Coolant – Blue x4 @ $20.00ea $80.00
AC38919 EKWB EK-Quantum Vector Strix RTX 3080/3090 D-RGB Nickel + Plexi GPU Water Block x1 $299.00
AC38928 EKWB EK-Quantum Vector Strix RTX 3070/3080/3090 Backplate – Black x1 $99.00
AC52280 Thermaltake Pacific MX1 Plus CPU Water Block x1 $169.00
AB61445 Thermaltake Pacific G1/4 Stop Plug w/ O-Ring – Black x4 @ $6.00ea $24.00
AB61458 Thermaltake Pacific G1/4 Female to Male 30mm extender – Black x3 @ $10.00ea $30.00
AB61450 Thermaltake Pacific 3/8” ID Barbs – Black x18 @ $7.00ea $126.00
AB61465 Thermaltake Pacific G1/4 90 Degree Adapter – Black x10 @ $15.00 $150.00
AC10340 Noctua Chromax.Black 30cm 4Pin PWM Power Extension Cables – 4 Pack x1 $15.00
AC11822 EKWB EK-Cable Y-Splitter 3-Fan PWM (10cm) x3 @ $7.99ea $23.97
From Amazon https://www.amazon.com.au/
PH-GB2080ASDEVO_CR01 Phanteks Glacier Dual Evo, Full GPU Water Block for ASUS RTX 2080/2070/2060 Super Dual EVO Series x1 $236.93
From PCCaseGear https://www.pccasegear.com/
3830046991737 EK M.2 NVMe Heatsink Black x2 @ $19.00ea $38.00
BN816 be quiet! Dark Power Pro 12 Titanium Modular 1200W Power Supply x1 $599.00
PC-O11DXL-A Lian Li PC-O11 Dynamic XL ROG Certified Case Silver x1 $319.00
8. But Why Don't You Just...
People suggest all sorts of extreme cooling loop designs online, such as massive external radiators, refrigerated coolant systems, running cooling pipes outside the house, running pipes into their swimming pool or underground through the cold earth, and so on. Undoubtedly many of these suggestions would improve the cooling capacity of the system. However, the aim of a standard water cooling loop is to fit within a PC case, be self-contained, to use readily available parts, to be cost effective and to be relatively easy to set up. If you want to experiment with crazy ideas after getting the basic cooling loop working, I say good luck and let me know how it goes! :D

9. Single versus Dual Loop
There may be advantages to having two separate cooling loops, one for the GPU(s) and one for the CPU. I have not experimented with this, but advice I have read suggests this may be better for CPU cooling, to keep the CPU temperatures lower than may be possible when the CPU shares a loop with the GPUs. A dual loop will increase the costs as you will need an additional pump and reservoir, at least one more radiator, and more fittings.
I got lucky as the AMD Ryzen 3900XT CPU is designed to run at high temperatures, so it is happy sharing a cooling loop with two GPUs. In my loop, the CPU runs at between 80C – 90C while at max processing load (this is within its max operating temperature range), with coolant water temperatures at about 35C while room temp is around 22C. These are not great numbers for CPUs that need to run cooler than 80C (apparently for ideal CPU cooling, the water temp should be closer to 5C – 10C over room temp while the CPU is at the load you expect to run it at). Keep in mind that the temperatures my CPU and GPUs are reaching are during high performance computing loads. Gaming use will rarely push components to such extremes.
10. How Many Radiators Do You Need?
This is a difficult question to answer as it depends on the radiator size/thickness, wattage of your CPU and GPU, fan type and speed, and so on. It's best to read some of the guides available online, and to do your own research once you know the max wattage of the devices you want to cool. There's various bits of advice out there and even water cooling wattage vs radiator size calculators available online. The EKWB system configurator can provide some estimates and parts suggestions (though of course, it's designed to sell you their gear, so just use it to get an idea of the size and kinds of parts you'll need).
I should note that my first try at the wattage and radiator size calculations suggested I'd get away with using a single Thermaltake Pacific CL360 360mm Radiator (64mm thickness, the thickest 120mm x 320mm radiator they make). It's a huge radiator, but I found it just couldn't cool my system by itself when the CPU and GPUs were running continuously at high load. However the guides I followed are all for gaming use, not for running your devices at max wattage 24/7. I found I had to effectively double the amount of radiator surface area (by adding two more 27mm thickness radiators) to sufficiently cool my system for research computing use.
When it comes to radiators, bigger is is better (in all dimensions), as surface area determines the rate at which a radiator can exchange energy with the air. Make sure your case can accommodate the planned number of radiators, plus the thickness of the fans installed on top of them.
11. AIO vs Custom Loop
An alternative to a custom water loop is the “AIO” or All-In-One cooler. AIOs are a radiator, tubing and pump, all pre-assembled and filled with coolant. You attach the module to your CPU or GPU, mount the radiator, and then don't have to buy or assemble any other parts. These can provide a quick and easy alternative to creating your own custom cooling loop.
The disadvantages of AIO coolers are that they may not suit high performance computing where the CPU And GPU are pushed to extremes, and you will need space to mount a separate radiator per device needing to be cooled, rather than having the option to cool a number of devices with a single cooling loop. You may also find the length of the pre-attached non-removable coolant tubes isn’t sufficient to reach between your CPU or GPU, and the mount point you have chosen for the radiator.
It may also be difficult to find an AIO cooler that will suit your particular GPU, especially if it is an older model. Separate water blocks are available for a far wider selection of GPUs. CPU AIO coolers tend to be more universal and fit a wide range of CPU socket types, so are easier to fit to older CPUs.
12. Flushing all parts out with Distilled Water
It is recommended to flush all water cooling components and tubing with distilled water before connecting them to your cooling loop and filling the system with coolant. This clears out any fine metal and plastic that may be left over from the manufacturing process, that might interfere with your water blocks or pump impeller, etc. Distilled water is usually available from supermarkets, as it is used in fabric cleaning and filling clothes irons, etc.
13. Temperature and Flow Monitor
As I touched on earlier, I believe a temperature and flow sensor are essential for a water cooling loop. The model I use is the Thermaltake Pacific TF2 Temperature and Flow Indicator – CL-W275-CU00SW-A.
This lets you keep track of exactly what is happening in your loop, and lets you work out precisely the pros and cons of any changes or additions you make to the loop.
These sensors are best combined with measurements from a simple room thermometer, and software that can track temperature, watts and load over time. If you record temperature values as you make changes to your system's configuration (fan speed, direction, cooling loop setup, etc) then you can see what changes are really improving your system's performance and temperature.
These monitors also protect against future failures, when they have an inbuilt alarm. You can then instantly be warned of low flow rates or high coolant temperatures.
 The combined reservoir and pump, with temperature and flow monitor.
The combined reservoir and pump, with temperature and flow monitor.
14. Tubing
Some advice on the tubes that carry the coolant through your coolant loop:
- Water cooling loops can be made with soft flexible tuning, or hard tubing. Soft is easier for experimenting. Hard looks better but is difficult to work with. Hard tubing can be made into 90 degree bends, while this is usually not possible with soft tubing (it tends to kink and collapse when bent too tightly), so you have to rely on separate right-angle adapters.
- While water cooling tubes come in a variety of widths, all the commercially available sizes dedicated to PC water cooling will do the same job. Tube width simply makes no difference to cooling performance. Just be sure that whatever tubes you buy fit the width required by your chosen fittings. And the size of your fittings will be determined by the cooling components you buy. Be sure to check that everything is compatible!
- For soft tubing connected by barb connectors, use clamps to keep the tubing secured to the barbs. I used household cable ties, but dedicated (and nicer looking) clamps can be purchased. Barbs hold on to soft tubes just fine without clamps, but I found that bumping the tubes can cause small brief leaks around the barbs. Clamps also give insurance in case loop temp accidentally exceeds 50C and your tubes become soft, which makes it easier for them to pop off barb fittings.
15. Fans and Airflow
- Radiator fans should ideally be “high static pressure” type, but if reducing noise is a high priority, regular low noise fans are fine.
- Air speed over the radiators can be set quite low, and the radiators will still perform quite effectively. This is how water cooling can be much quieter than air cooling alone.
- I have just three fans running at low speed (50% PWM) per radiator and have already hit the max cooling performance capability of the radiators at my room’s usual air temperature. After a certain point, more airflow won't mean more cooling.
- 140mm fans are not significantly quieter than 120mm fans at high speed, and they're all effectively the same volume levels at low speeds. I have 10x 120mm fans in my system all running at low speed and they're barely audible. In fact the loudest sound my PC makes now is some coil whine (more on that below). So don't obsess over 140mm fans for water cooling use. Going after 140mm fans and 140mm wide radiators will likely limit your space and case options, and increase costs, for no real gain.
- Fan direction over the radiators does matter, as I found by testing various configurations and measuring the water and component temperatures. But the direction matters only in terms of where the cool air comes from and where the hot air goes to. Set the fans and radiators up so that air moves from outside the case, moves over the radiators, and then exhausts inside the case. Fans could be in push or pull configuration to achieve this (before or after the radiator in the direction of air flow). You can also use push/pull combined configurations (fans on both sides of the radiator), but I think this is overkill.
- Never draw hot air from inside the case over the radiators or you will lose cooling performance. Some online guides will tell you this loss in performance doesn't matter. And perhaps it doesn't matter in a gaming setup. But for high performance work, you need to claw back every single degree Celsius of cooling in your water loop that you can.
- Outgoing hot air that has passed through the radiators and into your case must have somewhere to escape. It must be able to escape at least as fast as the inflow rate. 3 fans moving air into the case will need at least 3 fans moving it out. I also found that you can get away with a very wide hole as the outlet, such as the open side or front of a case. This may not be pretty, but helps cool the rig even further when it’s being pushed to the limit.
- You may read advice that suggests “positive pressure” should be maintained inside the case (outflow rate less than inflow rate) to reduce dust by forcing air to enter only via filtered inlets. But this compromises airflow performance and doesn't completely prevent dust entering the case anyway, even with filters. You'll be cleaning dust out regularly, regardless.
- Clean dust out regularly using compressed air (with an air compressor or canned air).
- When considering how to minimise dust that builds up in the case or on radiators, don’t worry about mitigating this with fan direction, or fan/radiator order. You should be regularly cleaning your case and its components with compressed air. Your case will quickly and easily be made dust free after this kind of cleaning, so fan direction/placement for dust mitigation, or the presence/absence of filters, isn’t important.
- Remove all air filters from your case. Filters just restrict air flow and still don't prevent all dust entering the PC case, so you’ll be cleaning it anyway.
16. VRM, RAM, PCH and NVMe cooling
- What are all these acronyms? VRM: Voltage Regulator Module. These are part of many PC components. But it usually refers to the one on the motherboard beside the CPU. RAM: Random Access Memory. Just a fancy name for your PC’s memory sticks. PCH: Platform Controller Hub. May also be called a chipset. “This is the motherboard’s communications center and traffic controller”. NVMe: Non-Volatile Memory Express drive. Refers to the small solid-state hard drives that attach directly to the motherboard without cables.
- This point is often overlooked by people adding water cooling to their PC; Other components on your motherboard MUST have their own adequate airflow, or be water cooled. By adding a water cooling loop, you are very likely going to reduce the overall airflow over your motherboard. VRM, RAM, PCH and NVMe chips are all susceptible to overheating if this is not addressed. RAM and VRM in particular are designed to be cooled by air being moved by the CPU's air cooler, which will no longer be present when a CPU water block is installed.
- Water cooling blocks are available for all these devices, but VRM water blocks in particular can be tricky to find for your exact motherboard. So air cooling your VRM is easier.
- Having a dedicated fan or two blowing over the VRM, RAM and other botherboard components, set on low speed, should be adequate to cool them. Careful placement of the radiator(s) can allow radiator fans to additionally cool the VRM and RAM.
- RAM heatsinks are essential when using them for high performance computing, but most RAM comes with some kind of heatsink these days.
- NVMe drive heatsinks are recommended due to the potentially reduced airflow inside the case. These little devices can get quite hot under heavy use!
17. Reservoir and Pump
- The water coolant reservoir doesn't need to be big. It just needs to contain enough coolant to keep the pump wet, and to make priming the new loop easier. A bigger reservoir will not improve cooling performance.
- The water pump does not need to be at lowest point in the system, contrary to popular advice. It just needs to be installed lower than the reservoir, so the reservoir can keep it fed with coolant using gravity alone. This will assist with pump priming and lubrication. In the event of a leak, the placement of the pump will be meaningless, as the pump will happily eject all your coolant via the leak, and then run completely dry, regardless of where it is placed.
- When first priming the system with coolant, the radiators and water blocks will be full of trapped air bubbles. This air impedes cooling performance. However, over time the trapped air will be forced into the reservoir, where you can then let it escape via the filling plug. Run the pump at full speed for a couple of days (even while using the PC is fine) and you will find the trapped air will largely disappear. Tilting the PC case to extreme angles while running the pump will also help remove trapped air.
- The water pump does not need to be run at max speed, except when first clearing the system of trapped air. Once the air bubbles have been chased out, you can experiment with lower pump speed settings. Lower the speed in small increments and let the system run for 10-20 minutes. Keep doing this until you notice the water and device temperatures rising. Then you have found your optimum pump speed. This will help reduce pump noise, and power consumption.
18. Coolant
- Buying a pre-mixed coolant from a trusted brand and supplier is the best option. This is easier than mix-your-own coolant kits, and less prone to mistakes. I found that even in my unusually long coolant loop, having about 4 litres of coolant was plenty to let me fill it, and have some spare for the next coolant change and refill.
- Drain and replace your coolant every 6 months. Failure to do so will risk rusting and other fouling/failure of the cooling parts, even when it contains anti-rust and anti-algal agents.
- You can try designing your loop so there's a single low point with a drain valve to make replacing coolant easier. I didn't bother with this, however, and I don't find draining my system too much of a hassle. You just need to have towels ready to protect your PC components, and a decent sized plastic container strategically positioned, when you break open the connections to drain the liquid.
19. RGB Lighting
- Just about every computer component comes with RGB lighting these days. Water cooling parts are no exception. There's almost no avoiding it.
- RGB lighting is mostly pointless, but does look cool!
- It uses energy, which could be considered wasteful.
- It actually generates a small amount of heat, especially when you have dozens of RGB lit components. Some of this heat comes from the power supplies and circuitry driving the RGB lighting. It's not a lot of extra heat, but it will add to your overall system temperature. You may find it best to turn off the lighting when using the system for high performance computing. Or don't! It's sparkly. Ooooooh.
- RGB controllers and lights are driven by multiple different software packages, and each brand seems to have its own standards that don't quite interconnect with other brands. The range of software you need to control everything in a single system can be a pain. Universal control software exists, but nothing supports every single RGB component out there. You could make sure all your components are the same brand and/or use the same RGB connector standards, but this can artificially limit your loop design options.
- RGB lighting requires SO MANY CABLES, and different plug standards and RGB controller modules to install, route, etc. Every single RGB lit thing has an extra RGB cable dangling from it that will need to be routed inside your case and plug in somewhere.
20. Coil Whine
- Coil whine is usually a high pitched buzzing or ringing sound that comes from electronic components under heavy load. It's caused by coils that are part of voltage regulators and converters vibrating at audible frequencies. Coil whine is most typically heard from PSUs, Motherboards and GPUs.
- Coil whine can be mitigated by clever circuit design, and quality components, but the consumer electronics industry thinks we're used to it and that we tolerate it, so they don't have much incentive to spend the R&D dollars or manufacturing costs to remove coil whine completely.
- Remember when manufacturers used to tell us dead pixels were “acceptable” on LCD monitors? That seems laughable now. Consumer pressure does work. Excessive coil whine is something that can become unacceptable in new hardware if enough of us complain to the suppliers and manufacturers about it, RMA extremely whiny devices, and avoid buying products renowned for high levels of coil whine. Be sure to research your next GPU choice thoroughly! :)
- Unfortunately, coil whine is currently a fact of life when pushing GPUs and motherboards to the extreme (and is often heard even during normal gaming). Most GPUs will exhibit coil whine, but it can range anything from barely perceptible with the PC case open, to catastrophically loud even with the case closed.
- Coil whine from GPUs may improve with the use of water cooling, possibly because the water block clamps down on noisy coils and reduces the vibrations, or because it changes the specific operating temperatures and load conditions which caused the coil to whine in the first place.
- Existing coil whine in your system can actually be more audible when switching to water cooling, as it reduces the fan noise that may once have been masking the sound.
- Coil whine can be mitigated by moving the PC case further away from the sitting position if possible, changing the case orientation, or choosing a case well known for its ability to muffle sounds (though beware that “soundproofed” cases often have poor airflow). Anyone who typically wears headphones while using the PC is unlikely to have much issue with coil whine.
- My ASUS ROG Strix RTX3090 and Gigabyte RTX2060 Super GPUs both have audible coil whine when running at max power consumption. The PC case is on my desk right next to my seating position, with one of the side panels always open, so the whining sound is noticeable. The fans in the system run so quiet that coil whine is the primary sound I'm aware of coming from the PC case on a day to day basis. I have become used to the sound, and it doesn't bother me. But I thought this was an important issue to mention as it is a potential negative of high performance PC use, that can be annoying for some people.
Ashley Flynn – Games and Simulations Software Engineer Portfolio and contact – https://ajflynn.io/